20 KiB
title, shortTitle, intro, product, permissions, versions, miniTocMaxHeadingLevel, redirect_from, type, topics
| title | shortTitle | intro | product | permissions | versions | miniTocMaxHeadingLevel | redirect_from | type | topics | |||||||||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| Managing code scanning alerts for your repository | Manage alerts | From the security view, you can view, fix, dismiss, or delete alerts for potential vulnerabilities or errors in your project's code. | {% data reusables.gated-features.code-scanning %} | If you have write permission to a repository you can manage {% data variables.product.prodname_code_scanning %} alerts for that repository. |
|
3 |
|
how_to |
|
{% data reusables.code-scanning.beta %}
About alerts from {% data variables.product.prodname_code_scanning %}
You can set up {% data variables.product.prodname_code_scanning %} to check the code in a repository using the default {% data variables.product.prodname_codeql %} analysis, a third-party analysis, or multiple types of analysis. When the analysis is complete, the resulting alerts are displayed alongside each other in the security view of the repository. Results from third-party tools or from custom queries may not include all of the properties that you see for alerts detected by {% data variables.product.company_short %}'s default {% data variables.product.prodname_codeql %} analysis. For more information, see "Setting up {% data variables.product.prodname_code_scanning %} for a repository."
By default, {% data variables.product.prodname_code_scanning %} analyzes your code periodically on the default branch and during pull requests. For information about managing alerts on a pull request, see "Triaging {% data variables.product.prodname_code_scanning %} alerts in pull requests."
{% data reusables.code-scanning.upload-sarif-alert-limit %}
About alerts details
Each alert highlights a problem with the code and the name of the tool that identified it. You can see the line of code that triggered the alert, as well as properties of the alert, such as the severity{% ifversion fpt or ghes > 3.1 or ghae-issue-4697 or ghec %}, security severity,{% endif %} and the nature of the problem. Alerts also tell you when the issue was first introduced. For alerts identified by {% data variables.product.prodname_codeql %} analysis, you will also see information on how to fix the problem.
If you set up {% data variables.product.prodname_code_scanning %} using {% data variables.product.prodname_codeql %}, this can also detect data-flow problems in your code. Data-flow analysis finds potential security issues in code, such as: using data insecurely, passing dangerous arguments to functions, and leaking sensitive information.
When {% data variables.product.prodname_code_scanning %} reports data-flow alerts, {% data variables.product.prodname_dotcom %} shows you how data moves through the code. {% data variables.product.prodname_code_scanning_capc %} allows you to identify the areas of your code that leak sensitive information, and that could be the entry point for attacks by malicious users.
About severity levels
Alert severity levels may be Error, Warning, or Note.
By default, any code scanning results with a severity of error will cause check failure. {% ifversion fpt or ghes > 3.1 or ghae-issue-4697 or ghec %}You can specify the severity level at which pull requests that trigger code scanning alerts should fail. For more information, see "Defining the severities causing pull request check failure."{% endif %}
{% ifversion fpt or ghes > 3.1 or ghae-issue-4697 or ghec %}
About security severity levels
{% data variables.product.prodname_code_scanning_capc %} displays security severity levels for alerts that are generated by security queries. Security severity levels can be Critical, High, Medium, or Low.
To calculate the security severity of an alert, we use Common Vulnerability Scoring System (CVSS) data. CVSS is an open framework for communicating the characteristics and severity of software vulnerabilities, and is commonly used by other security products to score alerts. For more information about how severity levels are calculated, see the blog post.
By default, any code scanning results with a security severity of Critical or High will cause a check failure. You can specify which security severity level for code scanning results should cause a check failure. For more information, see "Defining the severities causing pull request check failure."{% endif %}
About labels for alerts that are not found in application code
{% data variables.product.product_name %} assigns a category label to alerts that are not found in application code. The label relates to the location of the alert.
- Generated: Code generated by the build process
- Test: Test code
- Library: Library or third-party code
- Documentation: Documentation
{% data variables.product.prodname_code_scanning_capc %} categorizes files by file path. You cannot manually categorize source files.
Here is an example from the {% data variables.product.prodname_code_scanning %} alert list of an alert marked as occuring in library code.
On the alert page, you can see that the filepath is marked as library code (Library label).
Viewing the alerts for a repository
Anyone with read permission for a repository can see {% data variables.product.prodname_code_scanning %} annotations on pull requests. For more information, see "Triaging {% data variables.product.prodname_code_scanning %} alerts in pull requests."
You need write permission to view a summary of all the alerts for a repository on the Security tab.
By default, the code scanning alerts page is filtered to show alerts for the default branch of the repository only.
{% data reusables.repositories.navigate-to-repo %} {% data reusables.repositories.sidebar-security %} {% data reusables.repositories.sidebar-code-scanning-alerts %} {% ifversion fpt or ghes > 3.1 or ghae-next or ghec %}
- Optionally, use the free text search box or the drop-down menus to filter alerts. For example, you can filter by the tool that was used to identify alerts.
 {% endif %}
{% data reusables.code-scanning.explore-alert %}
{% ifversion fpt or ghes > 3.1 or ghae-next or ghec %}
{% endif %}
{% data reusables.code-scanning.explore-alert %}
{% ifversion fpt or ghes > 3.1 or ghae-next or ghec %}
 {% else %}
{% else %}
 {% endif %}
{% endif %} - Optionally, if the alert highlights a problem with data flow, click Show paths to display the path from the data source to the sink where it's used.

- Alerts from {% data variables.product.prodname_codeql %} analysis include a description of the problem. Click Show more for guidance on how to fix your code.

{% ifversion fpt or ghes > 3.1 or ghae-next or ghec %} {% note %}
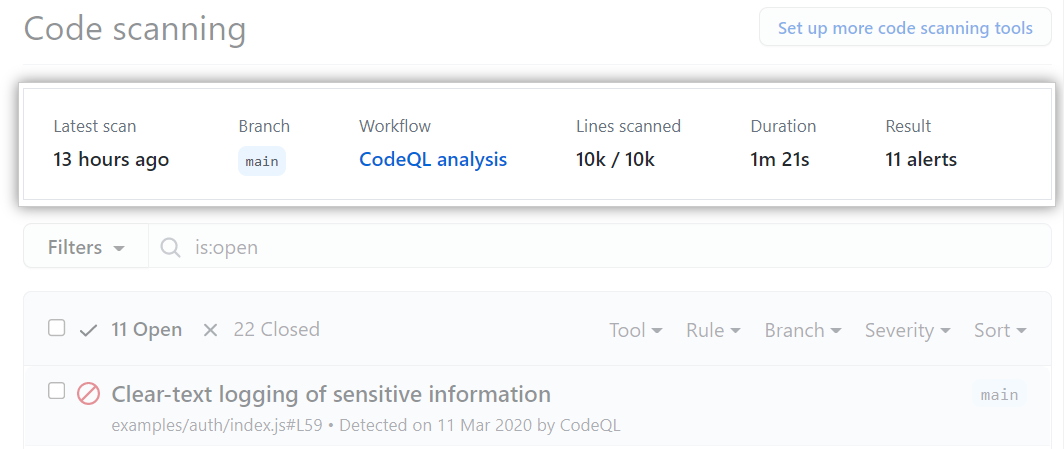
Note: For {% data variables.product.prodname_code_scanning %} analysis with {% data variables.product.prodname_codeql %}, you can see information about the latest run in a header at the top of the list of {% data variables.product.prodname_code_scanning %} alerts for the repository.
For example, you can see when the last scan ran, the number of lines of code analyzed compared to the total number of lines of code in your repository, and the total number of alerts that were generated.
{% endnote %} {% endif %}
Filtering {% data variables.product.prodname_code_scanning %} alerts
You can filter the alerts shown in the {% data variables.product.prodname_code_scanning %} alerts view. This is useful if there are many alerts as you can focus on a particular type of alert. There are some predefined filters and a range of keywords that you can use to refine the list of alerts displayed.
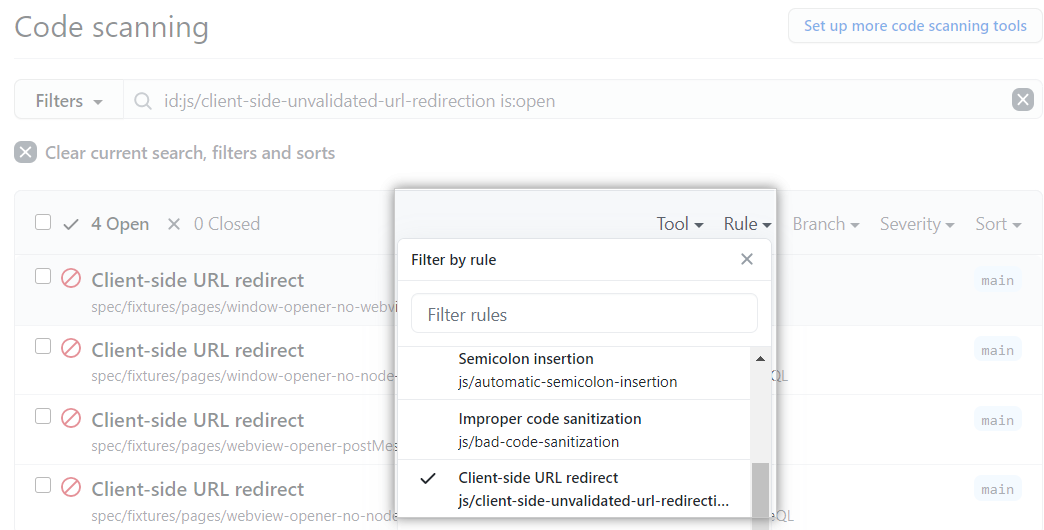
- To use a predefined filter, click Filters, or a filter shown in the header of the list of alerts, and choose a filter from the drop-down list.
{% ifversion fpt or ghes > 3.0 or ghec %}
 {% else %}
{% else %} {% endif %}
{% endif %} - To use a keyword, either type directly in the filters text box, or:
The benefit of using keyword filters is that only values with results are shown in the drop-down lists. This makes it easy to avoid setting filters that find no results.
If you enter multiple filters, the view will show alerts matching all these filters. For example, is:closed severity:high branch:main will only display closed high-severity alerts that are present on the main branch. The exception is filters relating to refs (ref, branch and pr): is:open branch:main branch:next will show you open alerts from both the main branch and the next branch.
Restricting results to application code only
You can use the "Only alerts in application code" filter or autofilter:true keyword and value to restrict results to alerts in application code. See "About labels for alerts not in application code" above for more information about the types of code that are not application code.
{% ifversion fpt or ghes > 3.1 or ghec %}
Searching {% data variables.product.prodname_code_scanning %} alerts
You can search the list of alerts. This is useful if there is a large number of alerts in your repository, or if you don't know the exact name for an alert for example. {% data variables.product.product_name %} performs the free text search across:
- The name of the alert
- The alert description
- The alert details (this also includes the information hidden from view by default in the Show more collapsible section)
| Supported search | Syntax example | Results |
|---|---|---|
| Single word search | injection |
Returns all the alerts containing the word injection |
| Multiple word search | sql injection |
Returns all the alerts containing sql or injection |
| Exact match search (use double quotes) |
"sql injection" |
Returns all the alerts containing the exact phrase sql injection |
| OR search | sql OR injection |
Returns all the alerts containing sql or injection |
| AND search | sql AND injection |
Returns all the alerts containing both words sql and injection |
{% tip %}
Tips:
- The multiple word search is equivalent to an OR search.
- The AND search will return results where the search terms are found anywhere, in any order in the alert name, description, or details.
{% endtip %}
{% data reusables.repositories.navigate-to-repo %} {% data reusables.repositories.sidebar-security %} {% data reusables.repositories.sidebar-code-scanning-alerts %}
- To the right of the Filters drop-down menus, type the keywords to search for in the free text search box.

- Press return. The alert listing will contain the open {% data variables.product.prodname_code_scanning %} alerts matching your search criteria.
{% endif %}
{% ifversion fpt or ghes > 3.3 or ghae-issue-5036 %}
Tracking {% data variables.product.prodname_code_scanning %} alerts in issues
{% data reusables.code-scanning.beta-alert-tracking-in-issues %} {% data reusables.code-scanning.github-issues-integration %} {% data reusables.code-scanning.alert-tracking-link %}
{% endif %}
Fixing an alert
Anyone with write permission for a repository can fix an alert by committing a correction to the code. If the repository has {% data variables.product.prodname_code_scanning %} scheduled to run on pull requests, it's best to raise a pull request with your correction. This will trigger {% data variables.product.prodname_code_scanning %} analysis of the changes and test that your fix doesn't introduce any new problems. For more information, see "Configuring {% data variables.product.prodname_code_scanning %}" and "Triaging {% data variables.product.prodname_code_scanning %} alerts in pull requests."
If you have write permission for a repository, you can view fixed alerts by viewing the summary of alerts and clicking Closed. For more information, see "Viewing the alerts for a repository." The "Closed" list shows fixed alerts and alerts that users have dismissed.
You can use{% ifversion fpt or ghes > 3.1 or ghae-next or ghec %} the free text search or{% endif %} the filters to display a subset of alerts and then in turn mark all matching alerts as closed.
Alerts may be fixed in one branch but not in another. You can use the "Branch" drop-down menu, on the summary of alerts, to check whether an alert is fixed in a particular branch.
{% ifversion fpt or ghes > 3.1 or ghae-next or ghec %}
 {% else %}
{% else %}
 {% endif %}
{% endif %}
Dismissing or deleting alerts
There are two ways of closing an alert. You can fix the problem in the code, or you can dismiss the alert. Alternatively, if you have admin permissions for the repository, you can delete alerts. Deleting alerts is useful in situations where you have set up a {% data variables.product.prodname_code_scanning %} tool and then decided to remove it, or where you have configured {% data variables.product.prodname_codeql %} analysis with a larger set of queries than you want to continue using, and you've then removed some queries from the tool. In both cases, deleting alerts allows you to clean up your {% data variables.product.prodname_code_scanning %} results. You can delete alerts from the summary list within the Security tab.
Dismissing an alert is a way of closing an alert that you don't think needs to be fixed. {% data reusables.code-scanning.close-alert-examples %} You can dismiss alerts from {% data variables.product.prodname_code_scanning %} annotations in code, or from the summary list within the Security tab.
When you dismiss an alert:
- It's dismissed in all branches.
- The alert is removed from the number of current alerts for your project.
- The alert is moved to the "Closed" list in the summary of alerts, from where you can reopen it, if required.
- The reason why you closed the alert is recorded.
- Next time {% data variables.product.prodname_code_scanning %} runs, the same code won't generate an alert.
When you delete an alert:
- It's deleted in all branches.
- The alert is removed from the number of current alerts for your project.
- It is not added to the "Closed" list in the summary of alerts.
- If the code that generated the alert stays the same, and the same {% data variables.product.prodname_code_scanning %} tool runs again without any configuration changes, the alert will be shown again in your analysis results.
To dismiss or delete alerts:
{% data reusables.repositories.navigate-to-repo %} {% data reusables.repositories.sidebar-security %} {% data reusables.repositories.sidebar-code-scanning-alerts %}
-
If you have admin permissions for the repository, and you want to delete alerts for this {% data variables.product.prodname_code_scanning %} tool, select some or all of the check boxes and click Delete.
Optionally, you can use{% ifversion fpt or ghes > 3.1 or ghae-next or ghec %} the free text search or{% endif %} the filters to display a subset of alerts and then delete all matching alerts at once. For example, if you have removed a query from {% data variables.product.prodname_codeql %} analysis, you can use the "Rule" filter to list just the alerts for that query and then select and delete all of those alerts.
{% ifversion fpt or ghes > 3.1 or ghae-next or ghec %}
 {% else %}
{% else %}
 {% endif %}
{% endif %}
- If you want to dismiss an alert, it's important to explore the alert first, so that you can choose the correct dismissal reason. Click the alert you'd like to explore.
{% ifversion fpt or ghes > 3.1 or ghae-next or ghec %}
 {% else %}
{% else %}
 {% endif %}
{% endif %}
-
Review the alert, then click Dismiss and choose a reason for closing the alert.

{% data reusables.code-scanning.choose-alert-dismissal-reason %}
{% data reusables.code-scanning.false-positive-fix-codeql %}
Dismissing multiple alerts at once
If a project has multiple alerts that you want to dismiss for the same reason, you can bulk dismiss them from the summary of alerts. Typically, you'll want to filter the list and then dismiss all of the matching alerts. For example, you might want to dismiss all of the current alerts in the project that have been tagged for a particular Common Weakness Enumeration (CWE) vulnerability.





